After Days of DDoS, Now Ubuntu's Twitter Account Seems to be Compromised
It seems like Ubuntu cannot catch a break.
Their entire web infrastructure was under continued DDoS attack for 5 days. Which seemed to be over now. But the misery is not.
A few hours ago, there was a (now deleted) tweet from Ubuntu's official Twitter account. It announced the availability of Ubuntu's newest AI agent.
At first glance, it looked legit until you dug deeper.
Ubuntu's official Twitter account was compromised
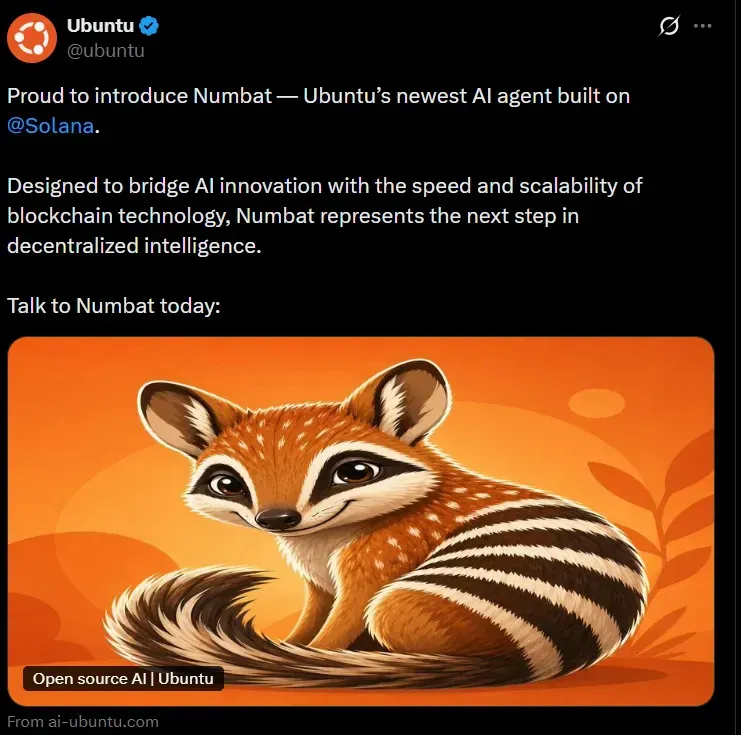
The tweet looks legit, right? At least it plays with the human psyche.
It talks about AI, which relates to Ubuntu's recent AI move. This could trick many people who might believe that this is a legit next step in the AI direction.
It was mentioned to be built on Solana and the account was also tagged. Solana is a legit open-source blockchain platform for digital transactions and decentralized applications (read crypto payments).
This is why the next line mentions buzzwords like Blockchain and decentralized. Blockchain also relates to crypto so this was more like a build up for crypto that would come later.
The so-called agent is called Numbat and the main image shows the Numbat animal with orange as its primary color. "Numbat" is also part of Ubuntu 24.04 codename Noble Numbat.
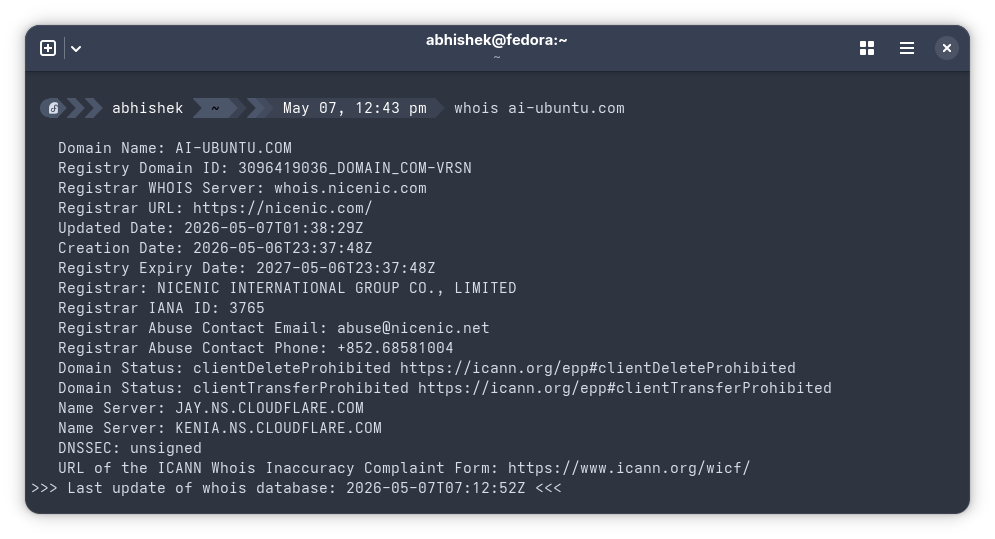
And then the displayed URL is ai-ubuntu.com which is similar to ai.ubuntu.com although ai subdomain doesn't exist on Ubuntu but it is enough to trick unsuspecting people.
Mind that it was not a single tweet; it was a thread (a series of nested tweets) and the replies were closed. So even if someone discovered the scam, they wouldn't have been able to alert others in the replies.
So, fake AI branding, Ubuntu's Numbat name, Solana tags, blockchain buzzwords, and a near-identical URL to quietly build false trust and thus guiding unsuspecting users step by step into a crypto scam before they realize the deception.
The next step of deception came when the link was clicked.
The crypto trap
Like most of the briefly compromised accounts, this tweet also tried to lure people into a crypto scam. It was not evident immediately unless you clicked on the given URL. And boy that URL looks like a typical Canonical webpage.
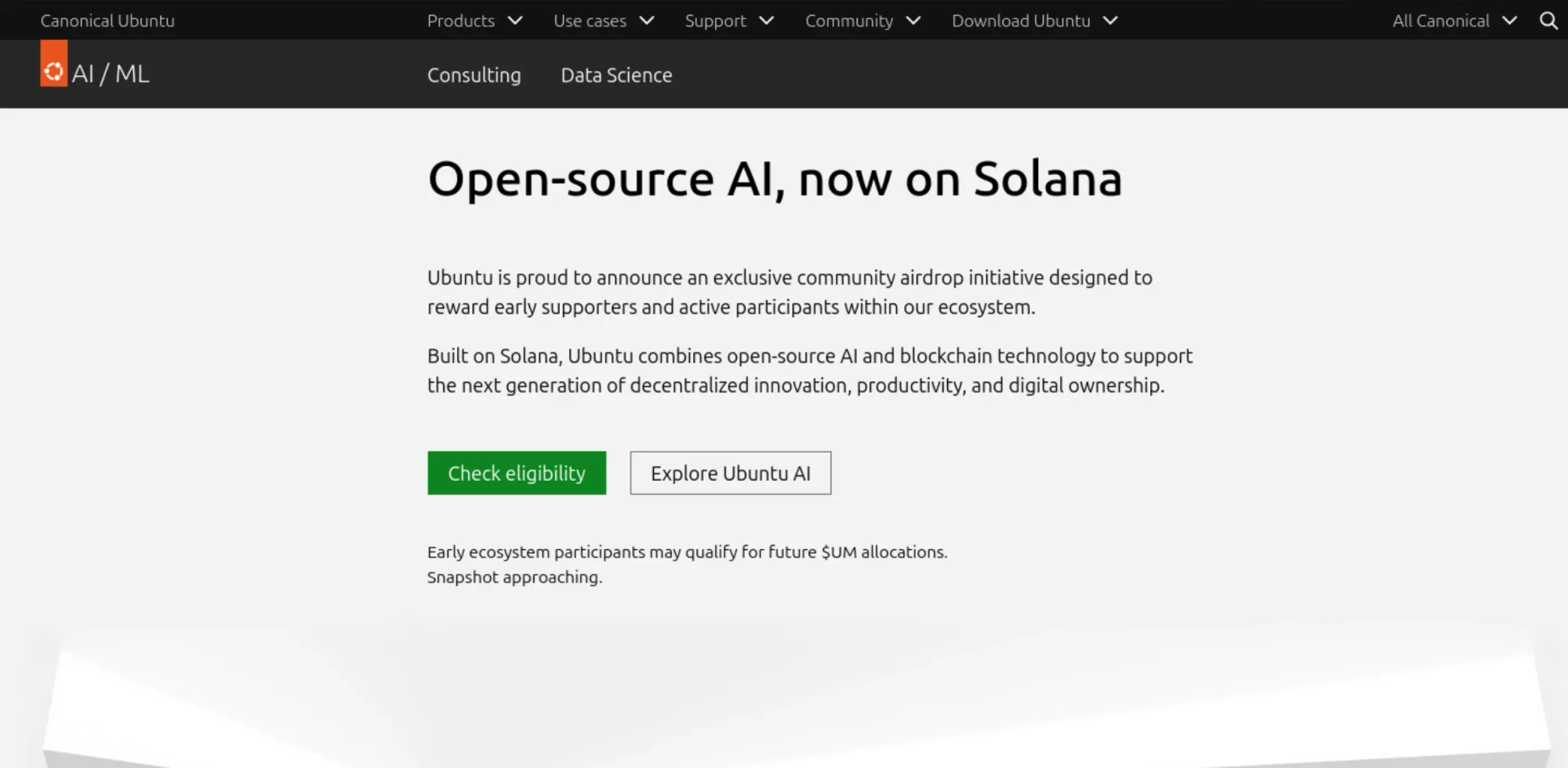
It is not impossible to get fooled by the clever webpage if you are not paying attention. Your guards would have been down because you clicked a link shared by official Ubuntu account.
The rest of the page had links to actual Ubuntu project and thus making it look even more legit.
It was only when you clicked the "Check eligibility" or "Explore Ubuntu AI" buttons, the deception was evident. It asked you to add your crypto wallet.
Why would you do that? Because just before the buttons, there is a text that says:
Early ecosystem participants may qualify for future $UM allocations. Snapshot approaching.
This compromised tweet just adds to the pile of misery Canonical had been suffering of late and it didn't happen in isolation.
The DDoS attack that crumbled Canonical's web assets
In case you didn't know, Ubuntu was suffering from a large scale DDoS attack. Ubuntu's websites went down for about five days last week but they seem to be back now.
Starting April 30, Canonical's web services faced what the company described as a "sustained, cross-border" attack. The ubuntu.com website, Snap store, Launchpad, and several other Canonical-owned services went offline or became unreliable.
The attack lasted until around May 5, when services were gradually restored. At the time of writing this, Canonical's official status page shows everything fully operational. Let's hope it stays that way.
Note that DDoS attacks make a website unavailable by flooding the server with traffic. It didn't compromise the servers. So, your Ubuntu installation, package updates (APT repositories are mirrored across the world and kept working), ISO downloads, and the Ubuntu operating system itself was not impacted. Your system was never at risk. Although, if you had trouble running snap install commands or pulling from a PPA last week, you now know why.
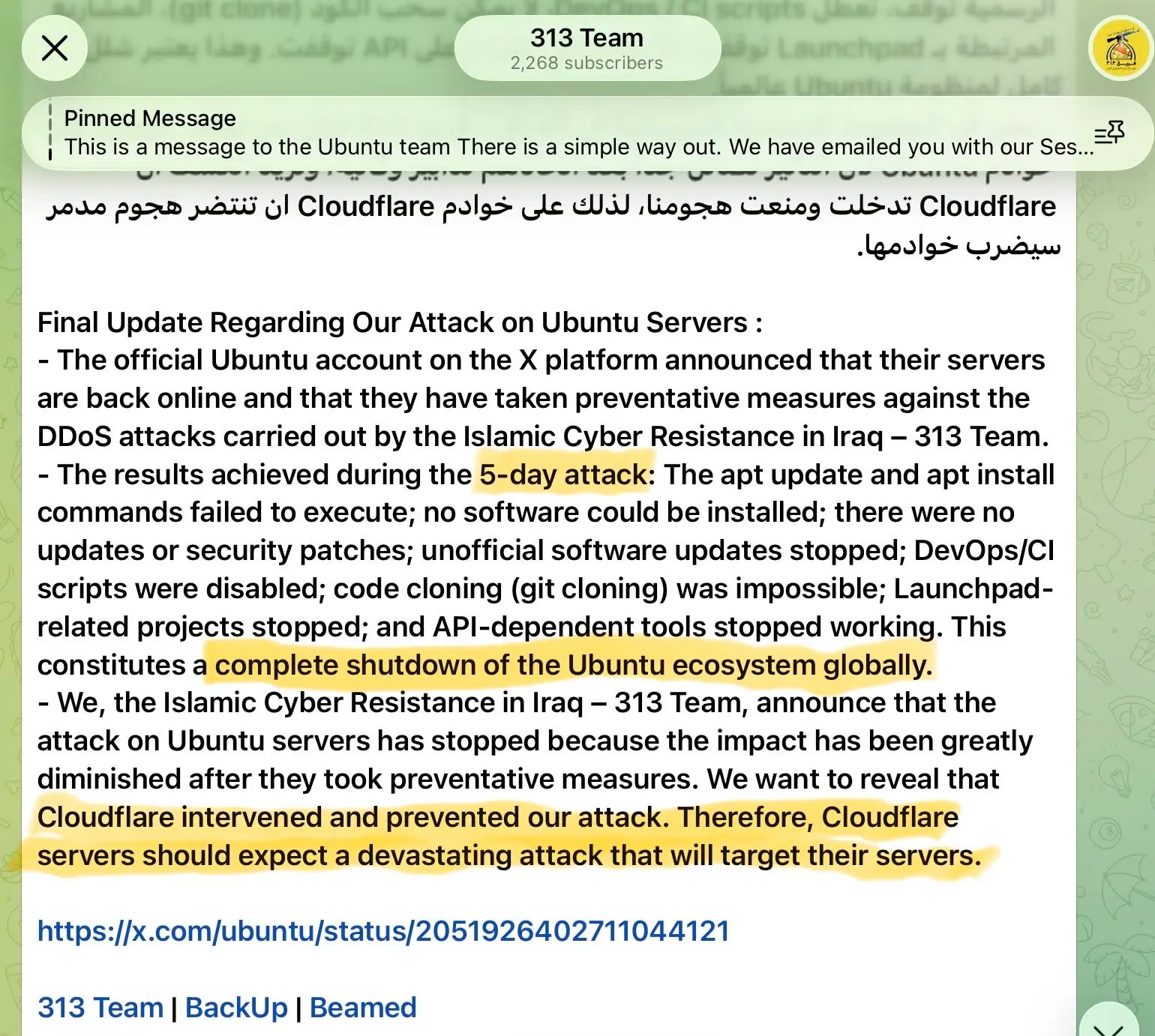
Canonical has not released a detailed post-incident report yet. A Pro-Iran hacker group called 313 reportedly claimed responsibility, but this has not been confirmed by Canonical.
Are both incidents are connected?
The hacker group 313 has announced that they have ended the DDoS attacks. They have not mentioned anything about compromised tweet.
Now, ai-ubuntu.com was registered with a Hong Kong based registrar, but that doesn't mean the attackers were based in Hong Kong.
One thing to note here is that many organizations as well as individual accounts often use third-party tools to manage and schedule their tweets. It is also possible that the compromise came from such a third-party Twitter tool. This could also be a human slip up and their social media manager's account might have compromised.
It is really up to Canonical to investigate and find out the root cause. We can only make guesses.
![]()
Source: It's FOSS